ASN / RPKI validity / BGP stats / IPv4v6 / Prefix / ASPath / Organization / IP reputation lookup tool.
This script serves the purpose of having a quick OSINT command line tool at disposal when investigating network data, which can come in handy in incident response scenarios as well.
Features:
- It will lookup relevant Autonomous System information for any given AS number, including:
- Organization name
- IXP Presence (Internet Exchange facilities where the AS is present)
- BGP statistics (neighbours count, originated v4/v6 prefix count)
- Peering relationships separated by type (upstream/downstream/uncertain), and sorted by observed path count, to give more reliable results (so for instance, the first few upstream peers are most likely to be transits).
- Announced prefixes aggregated to the most relevant less-specific
INET(6)NUMobject (actual LIR allocation).
- It will perform an AS path trace (using mtr in raw mode and retrieving AS data from the results) for single IPs or DNS results, optionally reporting detailed data for each hop, such as RPKI ROA validity, organization/network name, geographic location, etc.
- It will detect IXPs (Internet Exchange Points) traversed during the trace, and highlight them for clarity.
- It will attempt to lookup all relevant abuse contacts for any given IP or prefix.
- It will perform RPKI validity lookups for every possible IP. Data is validated against RIPE RPKI Validator. For path traces, the tool will match each hop's ASN/Prefix pair (retrieved from the Prefix Whois public server) with relevant published RPKI ROAs. In case of origin AS mismatch or unallowed more-specific prefixes, it will warn the user of a potential route leak / BGP hijack along with the offending AS in the path (requires
-doption, see below for usage info). - It will perform IP reputation lookups (especially useful when investigating foreign IPs from log files).
- It is possible to search by organization name in order to retrieve a list of IPv4/6 network ranges related to a given company. A multiple choice menu will be presented if more than one organization matches the search query.
- It is possible to search for ASNs matching a given name, in order to map the ASNs for a given organization.
Screenshots for every lookup option are below.
The script uses the following services for data retrieval:
Requires Bash v4.2+. Tested on:
- Linux
- FreeBSD
- Windows (WSL2, Cygwin)
- MacOS (thanks Antonio Prado and Alessandro Barisone)
- IPv4 lookup
- IPv4 lookup (bad reputation IP)
- IPv6 lookup
- Autonomous system number lookup with BGP stats, peering and prefix informations
- Hostname lookup
- ASPath trace to www.github.com
- ASPath trace traversing both an unannounced PNI prefix (FASTWEB->SWISSCOM at hop 11) and an IXP (SWISSCOM -> ROSTELECOM through DE-CIX at hop 14)
- Detailed ASPath trace to 8.8.8.8 traversing the Milan Internet Exchange (MIX) IXP peering LAN at hop 5
- Organization search for "github"
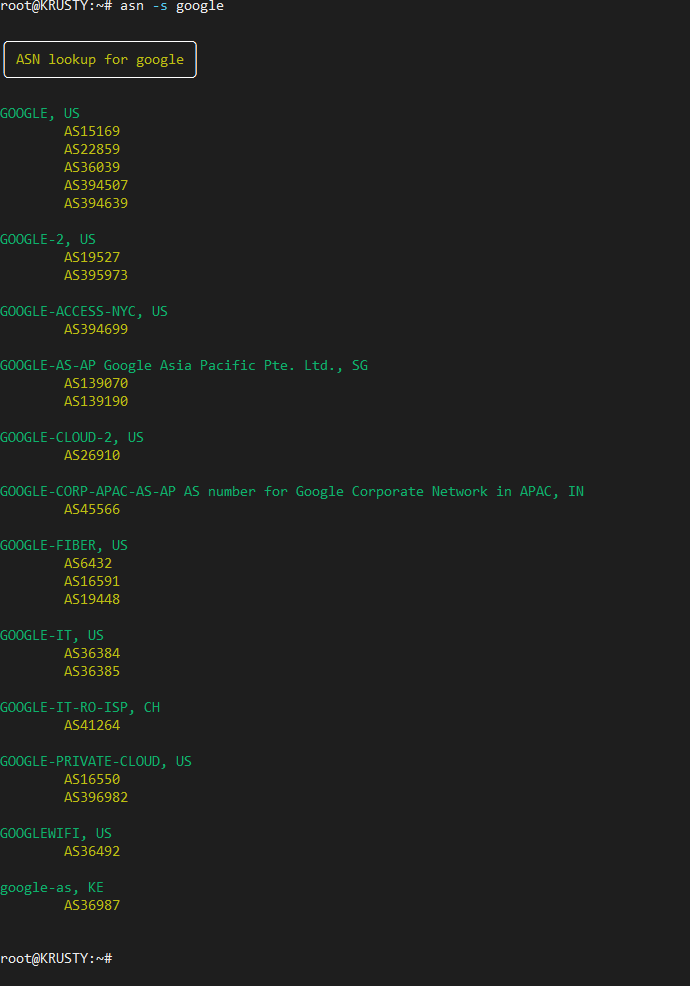
- Suggested ASNs for "google"
This script requires BASH v4.2 or later. Some additional packages are also required for full functionality:
-
Debian/Ubuntu:
apt -y install curl whois bind9-host mtr-tiny jq ipcalc grepcidr -
CentOS 7/8:
yum -y install curl whois bind-utils mtr jq perl && \ rpm -ivh http://www6.atomicorp.com/channels/atomic/centos/7/x86_64/RPMS/grepcidr-2.0-1.el7.art.x86_64.rpm \ https://ftp.tu-chemnitz.de/pub/linux/dag/redhat/el7/en/x86_64/rpmforge/RPMS/ipcalc-0.41-1.el7.rf.x86_64.rpm -
FreeBSD:
env ASSUME_ALWAYS_YES=YES pkg install bash coreutils curl whois mtr jq ipcalc grepcidr -
MacOS (using Homebrew):
brew install bash coreutils curl whois mtr jq ipcalc grepcidr && brew link mtr(Note for MacOS users: if
mtrstill can't be found after running the command above, this may help to fix it)
Afterwards, to download the asn script from your shell:
curl https://raw.githubusercontent.com/nitefood/asn/master/asn > asn && chmod +x asn
You can then use the script by running ./asn.
The script will perform anonymous IPv4/v6 IP reputation lookups without the need for an API token, using the Auth0 Signals API.
Nevertheless, it's strongly recommended to sign up for their service (it's free) and get an API token, which will raise the daily query quota from 100 hits to 40000 hits.
Once obtained, the api token should be written to the $HOME/.asn/signals_token file.
In order to do so, you can use the following command:
TOKEN="<your_token_here>"; mkdir "$HOME/.asn/" && echo "$TOKEN" > "$HOME/.asn/signals_token" && chmod -R 600 "$HOME/.asn/"
asn will pick up your token on the next run, and use it to query the Signals API.
asn <ASnumber>-- to lookup matching ASN and BGP announcements/neighbours data. Supports "as123" and "123" formats (case insensitive)asn [-n|-d] <IPv4/IPv6>-- to lookup matching route(4/6), IP reputation and ASN dataasn [-n|-d] <host.name.tld>-- to lookup matching IP(v4/v6), route and ASN data (supports multiple IPs - e.g. DNS RR)asn <Route>-- to lookup matching ASN data for the given prefixasn [-o] <Organization Name>-- to search by company name and lookup network ranges exported by (or related to) the companyasn [-s] <Name>-- to search for all ASNs matching a given name. Can be used to map all ASNs related to a given company
- AS path tracing is enabled by default for all lookups. In case of multiple IP results, the script will trace the first IP, with a preference for IPv6 if possible on the user's host.
- Geolocation and organization data is taken from pWhois, while IP reputation data is taken from Auth0 Signals.
- Tracing can be disabled altogether by passing the
[-n|--notrace]command line switch.
-
Detailed hop info reporting and RPKI validation can be turned on by passing the
[-d|--detailed]command line switch. This will enable querying the public pWhois server and the RIPE RPKI Validator for every hop in the mtr trace. Relevant info will be displayed as a "tree" below the hop data, in addition to Team Cymru's server output (which only reports the AS name that the organization originating the prefix gave to its autonomous system number). This can be useful to figure out more details regarding the organization's name, the prefix' intended designation, and even (to a certain extent) its geographical scope.Furthermore, this will enable a warning whenever RPKI validation fails for one of the hops in the trace, indicating which AS in the path is wrongly announcing (as per current pWhois data) the hop prefix, indicating a potential route leak or BGP hijacking incident.
- The script will try to figure out if the input is an Organization name (i.e. if it doesn't look like an IP address, an AS number or a hostname).
In order to force an organization search (for example for Orgs containing
.in their name), pass the[-o|--organization]command line switch.
- The script will try to find ASNs matching the given search string, using the RIPEStat API.
- The script will detect IXPs traversed during path traces by matching them with PeeringDB's comprehensive dataset of IXP prefixes.
- The script will also attempt a best-effort, fallback generic
whoislookup when Team Cymru, pWhois and PeeringDB have no info about the IP address or prefix. This is usually the case with some PNI prefixes, and will give better insight into the path taken by packets.
This script was featured in the Security Trails blog post "ASN Lookup Tools, Strategies and Techniques". Thank you Esteban!
Any feedback or pull request to improve the code is welcome. Feel free to contribute!